The “Invisible Corridor”
Security doesn’t break all at once; it erodes in the shadows. The alert didn’t appear to be a crisis because, to your perimeter, everything looked normal. An authorized user, a permitted port, and a standard protocol—on paper was a valid connection. In reality, it was the “keys to the kingdom” being handed over. This is the new reality of East-West traffic: the most dangerous threats aren’t trying to break in; they are already inside, moving through the invisible corridors of your network.
This is the new reality of the modern datacenter. It isn’t just about the “front door” anymore; it’s about the invisible corridors an attacker creates once they are already in. According to the Verizon 2025 Data Breach Investigations Report, ransomware was involved in 44% of all confirmed breaches last year. We have entered an era where attacks occur at machine speed; with some ransomware campaigns now completing in as little as 25 minutes, the traditional “human-in-the-loop” response is no longer fast enough. As documented in The Dawn of AI-Orchestrated Cyberattacks, when AI can autonomously execute 90% of an attack chain, defenders can no longer rely on manual triage. The consequences of this speed are devastating across every industry. From healthcare, where a single ransom payout can be dwarfed by a total operational impact exceeding $2 billion, to manufacturing, where a single breach can trigger billions in economic losses, the pattern is the same. Even iconic public institutions have been taken down for months, forced back to pen and paper. The message is clear: when attackers use AI and automation to move laterally, “good enough” security becomes an invitation for disaster.
The Gap: Why Traditional Security Fails
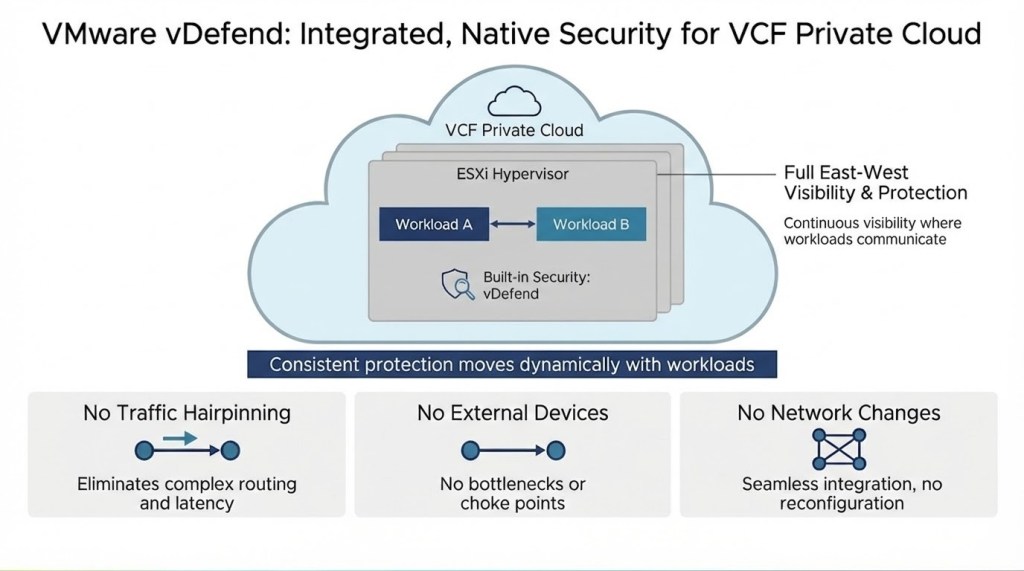
Traditional security models fail in the modern data center because they are architecturally blind to “East-West” traffic—the communication flowing between application workloads. To provide security, legacy models force this internal traffic out of the virtual layer and onto legacy hardware appliances, a process known as “hairpinning.” This inefficient routing creates massive network complexity by forcing convoluted VLAN management and halving link capacity, while these centralized security stacks become performance bottlenecks that introduce latency and application timeouts. Ultimately, these fragmented tool silos leave security teams with a patchwork of data, creating invisible corridors that allow attackers to move laterally and unchallenged across the private cloud.
The VMware vDefend Advantage
VMware vDefend eliminates the “blind spots” and performance penalties of traditional security by fundamentally changing the architecture of the defense. Rather than trying to pull traffic out of the virtual layer for inspection, vDefend embeds security directly into the hypervisor.
vDefend delivers integrated security by operating natively within the VCF private cloud. Every hypervisor acts as a built-in sensor, providing continuous visibility and protection where application workloads actually communicate. This architecture provides security teams with essential capabilities that external tools lack, including 360-degree visibility into both east-west and north-south traffic and consistent protection that moves dynamically with application workloads.
The Foundation: vDefend Distributed Firewall
Before addressing advanced threats, security starts with a hardened environment. The VMware vDefend Distributed Firewall (DFW) provides the essential structural foundation for Zero Trust. By moving security directly to the workload, the DFW enables precise microsegmentation that “shrinks” the attack surface, ensuring that if one VM is compromised, the threat is isolated.
To accelerate this journey, vDefend introduces the DFW 1-2-3-4 automated workflow built into the product. It is a prescriptive journey that moves you from initial visibility and “quick wins” (like securing DNS and NTP services) to full application-level microsegmentation in just a few weeks. Learn more about the DFW 1-2-3-4 approach here.
The Power of Closed-loop Security
However, walls alone—even virtual ones—are only half the story. While DFW answers, “Is this connection allowed?”, advanced threat prevention (ATP) answers the harder question: “Is this activity malicious?”
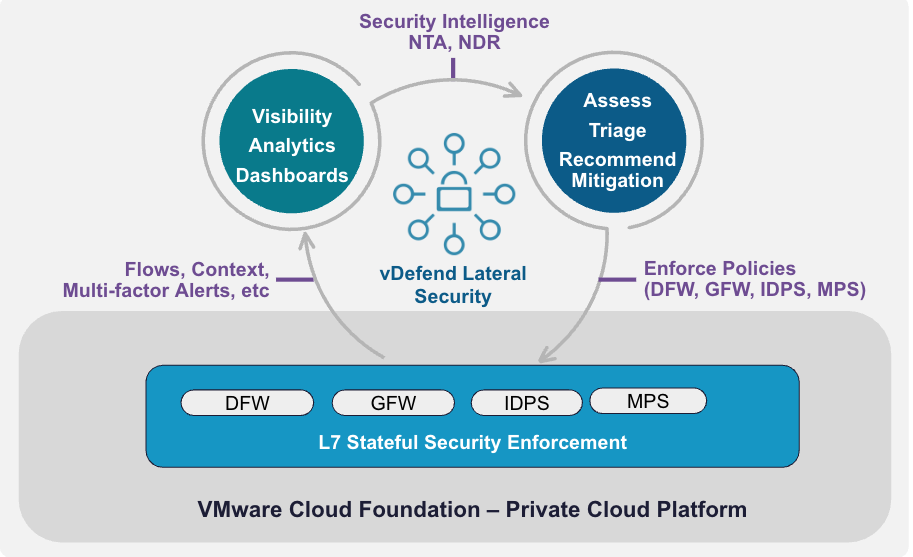
If DFW represents the structural strength of your vault—the steel doors and locked compartments—then ATP is the behavioral intelligence monitoring everything inside. Together, they create a closed-loop security that doesn’t just block known bad actors—it senses anomalies, isolates compromised assets, and neutralizes threats in one unified, automated motion.
vDefend: Hypervisor-Embedded Security
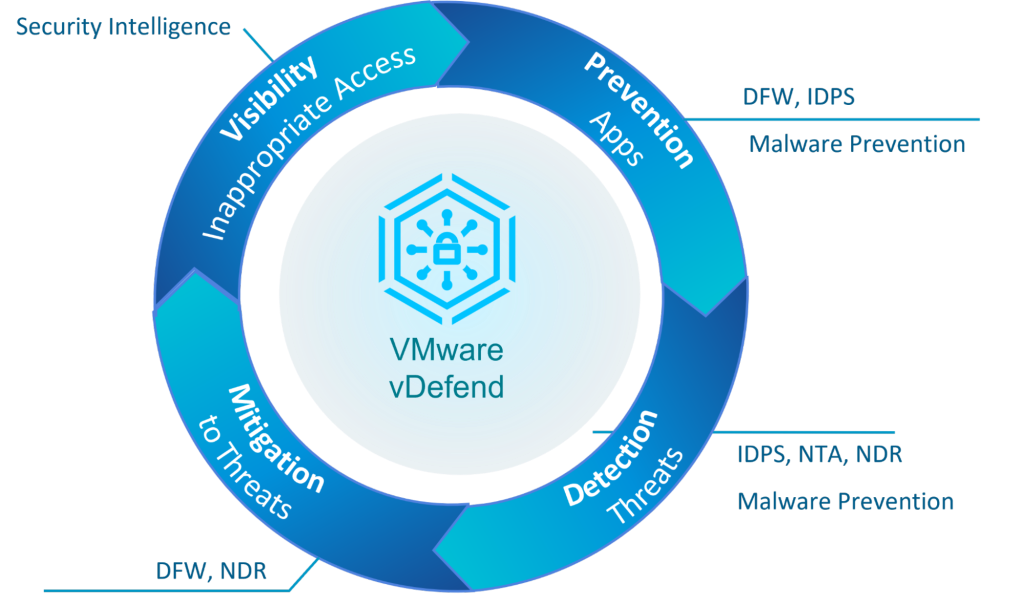
vDefend isn’t a bolt-on appliance; it is built directly into the ESXi hypervisor to disrupt the kill chain at every stage: Initial Access, Lateral Movement, and Encryption/Exfiltration. This approach allows us to disrupt the kill chain through four unified pillars aligned with the NIST cybersecurity framework:
1. Visibility: The All-Seeing Eye
Before you can defend, you must see. vDefend turns every hypervisor into a built-in sensor, providing ubiquitous visibility into the East-West corridor.
- Security Intelligence: Integrated directly with the DFW, Security Intelligence provides a real-time, interactive “flow-map” of your entire network. It automates application flow discovery and analyzes ingested data to provide ML-based firewall rule recommendations aligned with design best practices. This streamlines lateral security and accelerates the journey to a Zero Trust private cloud.
2. Prevention: Policy-Based Hardening
Prevention is about stopping the threat before it can take root in your environment.
- Microsegmentation (DFW Policies): The Distributed Firewall (DFW) acts as the first line of defense by enforcing a “Least Privilege” model. By dividing the network into granular, isolated segments, DFW ensures that only authorized traffic can flow between specific workloads.
- Distributed intrusion detection and prevention system (IDS/IPS): By inspecting every packet at the vNIC, we can “virtually patch” workloads. By blocking an exploit attempt for a known vulnerability at the network layer, the attack is neutralized at Stage 1.
- Malware Prevention (MPS): When an attacker attempts to download a malicious payload, MPS intervenes at the hypervisor I/O layer. We inspect the file before it is fully written to disk, preventing the infection from ever reaching the guest OS.
3. Detection: Behavioral Intelligence
When adversaries use zero-day exploits or stolen credentials, detection becomes the “behavioral brain” of your defense.
- Network Traffic Analysis (NTA): vDefend ATP monitors for the subtle “tells” of lateral movement—such as DNS Tunneling, DGA, or unusual protocol misuse. By establishing a baseline of normal network behavior, NTA identifies anomalies that signatures alone would miss.
- MPS/IDS Detection Mode: Even when active blocking is not yet enabled, running IDS and MPS in “Detect-Only” mode serves as a vital control. It provides the high-fidelity early warning needed to trigger a response before an attacker can escalate.
- Network Detection and Response (NDR): NDR acts as the centralized intelligence engine, automatically mapping detections from across the VCF network to the MITRE ATT&CK framework. It “stitches” together hundreds of isolated events into a Campaign—a single, navigable narrative that shows the entire attack chain from initial exploit to final exfiltration
4. Mitigation: Limiting the Damage
Mitigation is vDefend’s strategy for containing a breach and minimizing the “blast radius” once a threat is identified.
- Containment via Segmentation: While the firewall acts as a preventive gatekeeper, proper Microsegmentation is a powerful mitigation tool. If a VM is compromised, pre-defined segmentation rules contain the spread, preventing the attacker from reaching your “crown jewels.”
- Rapid Response Playbooks: Using the insights from NDR, a breach can be neutralized in seconds. For example, a suspicious endpoint can be automatically quarantined using security tags, instantly severing its ability to move laterally or communicate with external Command & Control (C2) servers.
This closed-loop security, from visibility, prevention, detection, to mitigation, is implemented through vDefend’s VCF integration in a unique way, as depicted in the diagram below.
vDefend: Why it Matters
In the traditional data center, security has often been a trade-off. Legacy security models force you to choose between deep protection and high performance. By embedding intelligence directly into VMware Cloud Foundation, vDefend eliminates that compromise.
- Operational Simplicity: No separate agents to manage. Security policies and firewall “states” move dynamically with your workloads.
- Reduced TCO: A software-defined, closed-loop security architecture significantly reduces CAPEX by eliminating the need for expensive hardware appliances.
- Integrated Solution: Distributed Firewall, IDS, MPS, NTA, and NDR all reside “under the same roof” within a single VCF management plane, eliminating the “swivel chair” effect between tools.
- Faster MTTD/MTTR: By correlating 1,000 noisy alerts into a single MITRE-aligned Campaign, we turn a mountain of data into an actionable story.
For more information on vDefend, watch the vDefend webinar series on demand here.