In September 2025, the cybercriminal group Storm-1175 exploited a zero-day vulnerability in GoAnywhere Managed File Transfer to deploy Medusa ransomware across multiple organizations. The attack succeeded despite perimeter defenses because no signature existed to detect it, and by the time one did, attackers had already established persistence and were moving freely through victim networks.
This incident illustrates a fundamental truth: perimeter firewalls alone cannot protect modern enterprises. Organizations must adopt a defense-in-depth strategy that provides visibility across every phase of an attack.
The Anatomy of a Zero-Day Attack
What Is a Zero-Day?
A zero-day vulnerability is a security flaw unknown to the vendor and the security community. Because no one knows it exists, no signature can detect its exploitation. These vulnerabilities are prized by threat actors precisely because they bypass traditional perimeter defenses.
According to CISA guidance, the most dangerous vulnerabilities, particularly those affecting widely-deployed shared services, are often kept secret by threat actors for extended periods. They remain “zero-day” until discovered by researchers or defenders, sometimes only after significant damage has occurred.
The GoAnywhere MFT Incident
On September 11, 2025, Microsoft Threat Intelligence observed Storm-1175 exploiting CVE-2025-10035, a critical deserialization vulnerability in GoAnywhere MFT’s License Servlet with a CVSS score of 10.0.
The timeline reveals the problem:
- September 11, 2025: Storm-1175 begins exploiting the vulnerability
- September 18, 2025: Fortra publishes security advisory
- September 18+, 2025: IDS signatures become available
For seven days, every organization running GoAnywhere MFT was vulnerable. No perimeter firewall could help, as there was nothing to detect.
Why Perimeter Defenses Failed
The Signature Problem
Perimeter firewalls rely on Intrusion Detection System (IDS) signatures to identify malicious traffic. These signatures are pattern-matching rules created by security researchers after a vulnerability becomes known.
This model has an unavoidable weakness: signatures are reactive. They cannot detect attacks using unknown vulnerabilities. When Storm-1175 exploited GoAnywhere MFT on September 11, there was no signature because no one outside the attacker group knew about the vulnerability.
Signatures Cannot Undo a Breach
Newly released detection signatures address future exploitation attempts; they do not remediate existing intrusions.
This limitation proved critical in the Storm-1175 intrusion. Microsoft’s analysis indicates that the threat actors established persistence mechanisms immediately following initial access, deploying:
- SimpleHelp and MeshAgent (legitimate remote monitoring tools)
- .jsp web shell files within the GoAnywhere MFT directories
Once these backdoors were in place, the attackers no longer needed the vulnerability. A signature detecting CVE-2025-10035 exploitation would catch future attacks, but the attackers were already inside, communicating through legitimate-looking channels.
Inside the Attack: What Happened After Initial Access
The Storm-1175 intrusion demonstrates how attackers operate once past the perimeter. Each phase was designed to evade detection by traditional security tools.
Phase 1: Persistence
The attackers dropped remote monitoring and management (RMM) tools directly under the GoAnywhere MFT process. SimpleHelp and MeshAgent are legitimate software used by IT departments worldwide. To a perimeter firewall, or even many endpoint tools, this looks like normal administrative activity.
Web shells (.jsp files) provided an additional backdoor, giving attackers persistent access to the compromised server even if the RMM tools were discovered.
Phase 2: Discovery
With persistence established, Storm-1175 began mapping the victim environment:
- User and system discovery commands identified accounts and system configurations
- Netscan deployment revealed the internal network topology
This reconnaissance happened entirely within the network perimeter. No external traffic to analyze. No signatures to trigger.
Phase 3: Command and Control
The attackers established a command-and-control infrastructure using two techniques specifically chosen to evade detection:
- RMM tools: SimpleHelp and MeshAgent traffic looks identical to legitimate IT administration
- Cloudflare tunnel: C2 communications were encrypted and routed through Cloudflare’s trusted content-delivery network
A perimeter firewall sees encrypted traffic to a reputable CDN provider. There is nothing inherently malicious about this pattern; hundreds of legitimate applications use Cloudflare daily.
Phase 4: Lateral Movement
This is where the attack becomes entirely invisible to perimeter defenses.
Storm-1175 used mstsc.exe, the built-in Windows Remote Desktop client, to move across systems within the compromised network. This east-west traffic never touches the perimeter. The firewall has no visibility into:
- A Confluence server connecting to the backup server via RDP
- That same server pivoting to the file server
- Subsequent connections to the domain controller and exchange server
The attackers moved freely through the network using a legitimate Windows tool over legitimate protocols.
Phase 5: Exfiltration
Before deploying ransomware, Storm-1175 exfiltrated data using Rclone, a command-line tool designed for syncing files to cloud storage. Rclone supports dozens of cloud providers and encrypts data in transit.
To a perimeter firewall, this looks like an employee backing up files to cloud storage, a routine, sanctioned activity in most organizations.
Phase 6: Ransomware Deployment
The attack culminated with the deployment of the Medusa ransomware across victim environments. By this point, the attackers had:
- Maintained access for days or weeks
- Mapped the entire network
- Compromised critical systems, including domain controllers
- Exfiltrated valuable data for double extortion
The ransomware deployment was the final, visible symptom of an infection that had spread silently through the organization.
The Need for Defense-in-Depth
The GoAnywhere MFT incident proves that perimeter-centric security creates a brittle defense. Once breached, whether through a zero-day vulnerability, stolen credentials, or a social engineering attack, threat actors operate with impunity if internal visibility is lacking.
Defense-in-depth addresses this by providing multiple detection opportunities across the attack lifecycle:
| Attack Phase | Perimeter Firewall | VMware vDefend Distributed Firewall (DFW) | VMware vDefend Distributed IDPS – part of VMware vDefend Advanced Threat Prevention (ATP) | VMware vDefend NTA/NDR (part of VMware vDefend ATP) |
|---|---|---|---|---|
| Initial exploit (zero-day) | None (no signature) | None | None (no signature) | Anomaly detection (limited) |
| Persistence (RMM tools, web shells) | None | None | Signature-based detection/prevention | Traffic anomaly to C2 |
| Discovery (netscan, enumeration) | None | Prevented in internal network using zero trust policy (DMZ only) | Signature-based detection | Scan pattern detection |
| Command and control (Cloudflare tunnel) | Encrypted/Legitimate | Prevented – Egress policy restriction | None (encrypted) | Tunnel/beaconing detection |
| Lateral movement (RDP) | None (internal traffic) | Prevented – Block RDP using zero trust infrastructure policies | Signature-based detection | RDP anomaly detection |
| Exfiltration (Rclone) | None (encrypted) | Prevented – Egress policy restriction | None (encrypted) | Anomalous upload detection |
| Ransomware deployment | None | Prevented in internal network (block SMB/RDP) with zero trust policies | None | SMB propagation detection |
Lateral Movement: The Critical Detection Point
Of all post-exploitation activities, lateral movement represents the most reliable detection opportunity. Here’s why:
- It must happen: Attackers rarely achieve their objectives from a single compromised host. They need to reach domain controllers, file servers, and backup systems.
- It creates observable patterns: Even when using legitimate tools like RDP, lateral movement generates anomalous traffic patterns. A web server initiating RDP connections to a backup server is unusual.
- It happens inside the network: Unlike C2 traffic, which can be tunneled through CDNs or encrypted channels, lateral movement occurs on the internal network, where organizations have full visibility.
The following is a breakdown of how each technology can help detect and prevent lateral movement attempts.
Distributed Firewall (DFW)
The VMware Distributed Firewall (DFW) can block lateral movement entirely by enforcing microsegmentation policies at the workload level. With DFW, even if an attacker compromises an application server, they cannot establish RDP, SMB, or other connections to systems outside their authorized communication scope. In the scenarios illustrated in Figures 2 and 3, a properly configured DFW policy would have blocked both the RDP connections, stopping the attack chain before lateral movement could occur.
Distributed IDPS
While NTA/NDR focuses on behavioral anomalies, a Distributed IDPS provides signature-based detection at every workload. Unlike traditional perimeter IDPS that only inspects north-south traffic, a distributed architecture applies intrusion detection to east-west traffic as well.
During lateral movement, attackers frequently use protocols and techniques with known signatures, such as exploitation of remote services, pass-the-hash attacks, or specific tool fingerprints. A Distributed IDPS can identify these patterns regardless of where they occur in the network.
Network Traffic Analysis / Network Detection and Response (NTA/NDR)
NTA/NDR solutions monitor east-west traffic precisely for lateral movement patterns. They establish behavioral baselines and identify anomalies that signature-based tools cannot detect. Key detection capabilities include:
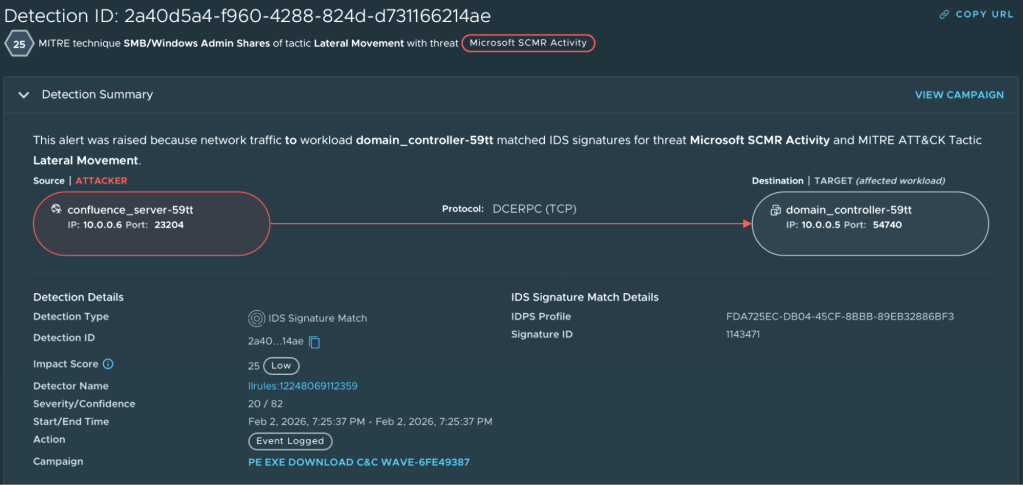
- Unusual authentication patterns between systems (lateral movement): For example, in vDefend ATP, the Intelligence component raises an alert when it detects MS-SCMR (Microsoft Service Control Manager Remote Protocol). Figure 2 shows an example of this detection when confluence_server-59tt tries to login into the domain_controller-59tt
Lateral Movement between Confluence Server and Domain Controller
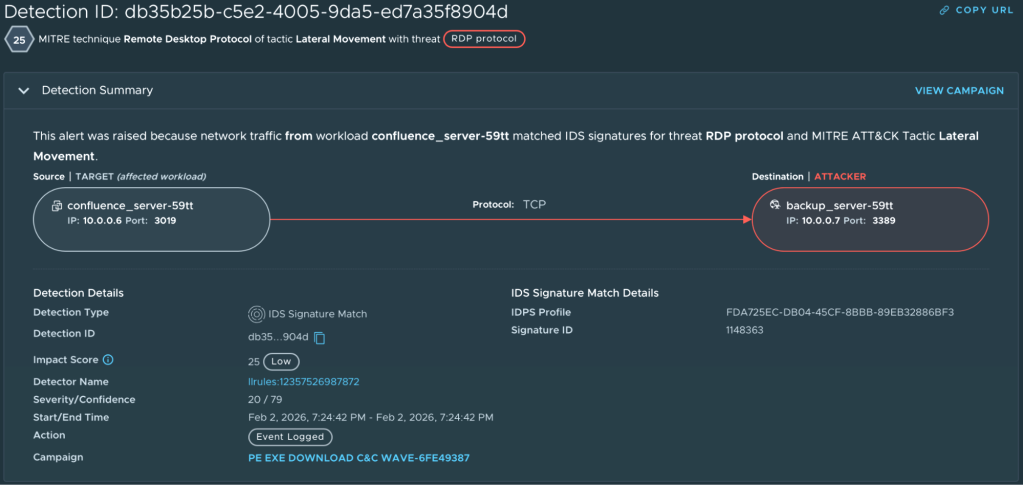
- Protocol anomalies (RDP from a server that has never initiated RDP): In vDefend ATP, the Intelligence component raises an alert when it detects an RDP connection within internal hosts. Figure 3 shows an alert raised when an RDP connection between confluence_server-59tt and backup_server-59tt was detected.
RDP connection from Confluence Server to Backup Server
- Credential abuse across multiple systems
- First-time connections between hosts
These behavioral indicators are invisible to perimeter firewalls but clearly visible to NTA/NDR solutions monitoring internal traffic flows.
The true value of NTA/NDR resides in improved triage capabilities that correlate individual events together into campaigns, enabling security teams to understand the full scope of an attack rather than investigating isolated alerts.
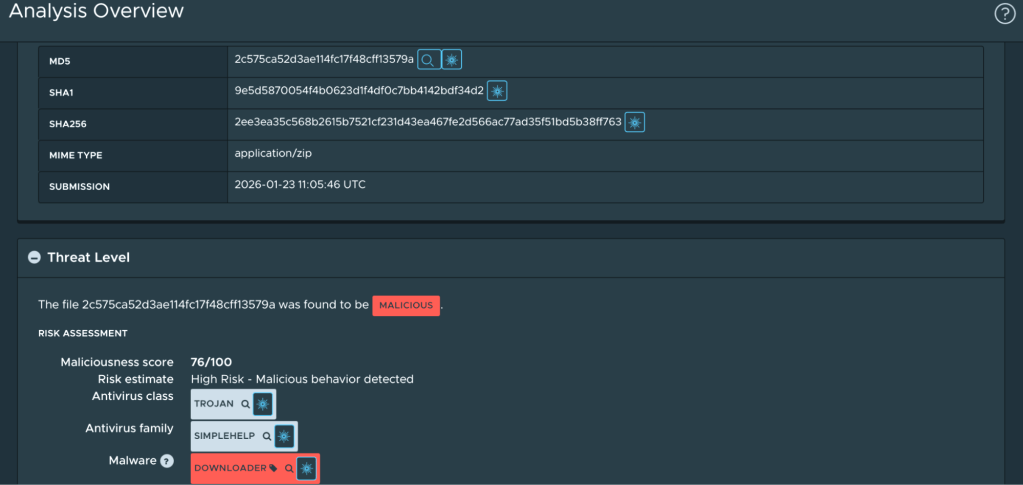
Sandbox Analysis
Furthermore, sandbox analysis provides visibility into attacker tooling and behavior. The ability to detonate suspicious samples in an isolated environment (see Figure 4) allows defenders to understand which tools the attacker executed and dropped in the environment.
Sandbox analysis for the SimpleHelp tool used by Storm-1175 for persistence
Without this layered internal visibility and enforcement capability, attackers like Storm-1175 move undetected from their initial foothold to complete network compromise.
Recommendations
Based on the GoAnywhere MFT incident and the broader threat landscape, organizations should:
Accept That Perimeter Breaches Will Occur
Zero-day vulnerabilities, stolen credentials, and sophisticated phishing will periodically succeed: Design your security architecture assuming the perimeter will be bypassed.
Segment Your Network
A compromised web server should never have direct RDP access to a domain controller. Implement network segmentation to restrict lateral movement opportunities and contain potential breaches.
Where possible, deploy macro- and microsegmentation using distributed firewalls to enforce least-privilege network access between workloads. Unlike traditional network segmentation that operates at the VLAN or subnet level, microsegmentation applies granular policies at the individual workload level, blocking unauthorized east-west traffic regardless of network topology.
In the Storm-1175 intrusion, attackers moved laterally via RDP from the initial compromised host to various workloads within the network. With microsegmentation policies in place, each of these connections would have been denied and logged.
Deploy Distributed Intrusion Detection and Prevention (DIDPS)
Unlike perimeter-based IDPS that only inspects north-south traffic, distributed IDPS operates at every workload, providing signature-based detection for lateral movement techniques such as MS-SCMR, PsExec, and exploitation attempts between internal hosts.
Deploy distributed IDPS to detect malicious activity that occurs entirely within the network perimeter.
Implement Network Traffic Analysis / Network Detection and Response (NTA/NDR)
NTA/NDR solutions monitor east-west traffic for behavioral anomalies that signature-based detection may miss. These include RDP connections from servers that have never initiated RDP, unusual authentication patterns, beaconing behavior indicative of C2 tunnels, and anomalous data transfers suggesting exfiltration.
Deploy NTA/NDR capabilities to identify attacker activity that leverages legitimate tools and encrypted channels.
Monitor for Legitimate Tool Abuse
Attackers increasingly use built-in operating system tools (mstsc.exe, PowerShell) and legitimate software (RMM tools, Rclone) to avoid detection.
Configure security tools to baseline normal behavior and generate alerts when anomalies occur.
Conclusion
The Storm-1175 intrusion against GoAnywhere MFT demonstrates why defense-in-depth is not optional. A sophisticated threat actor exploited a zero-day vulnerability, established persistence using legitimate tools, communicated through trusted infrastructure, and moved laterally using built-in Windows capabilities.
At every phase after initial access, the perimeter firewall was irrelevant. The attack unfolded entirely within networks that had no visibility into their own internal traffic and lacked the controls to prevent unauthorized lateral movement.
Organizations that rely solely on perimeter defenses are not asking if they will be breached, but when, and whether they will detect or prevent the attack before ransomware encrypts their systems.
The solution is defense-in-depth: layered security controls that provide detection opportunities at every phase of the attack lifecycle.
Distributed IDPS identifies malicious patterns at the workload level. Network Traffic Analysis detects anomalous lateral movement and command-and-control activity. The Distributed Firewall enforces microsegmentation policies that block unauthorized connections before they occur.
When the perimeter fails, internal visibility becomes the difference between a contained incident and a catastrophic breach.
To learn more about vDefend and its closed-loop security capabilities, read this blog.