In a cloud-native environment, Kubernetes-based containerized orchestration has brought developer agility – but it has also fundamentally changed the security paradigm. Traditional “castle-and-moat” security designs that rely on a perimeter firewall are no longer enough to protect modern workloads. Once an attacker breaches that outer shell, the flat network architecture common in many Kubernetes environments allows them to move laterally with ease, potentially compromising many applications in their hunt for high-value assets to ransom. The cyber landscape is further exacerbated by recent cyberattacks that have halted business operations for weeks and months, causing massive financial losses (hundreds of millions of dollars or more) and the emergence of AI-driven autonomous attacks.
Bridging this lateral security gap with VMware vDefend is crucial for organizations leveraging vSphere Kubernetes Service (VKS) within VMware Cloud Foundation (VCF). The fact that vDefend is fully integrated with VKS and completely plug-and-play with VCF makes a comprehensive rollout of Zero Trust lateral protection across all VKS clusters operationally simple and fast. Businesses can finally implement a true Zero Trust security model consistently across Virtual Machines and Containers – the same policy model, the same management console and APIs, the same troubleshooting tools. The powerful combination of vDefend with VKS Clusters decouples security policy from static, ephemeral IP addresses and instead uses workload-based identity to enforce granular protection.
In a typical Kubernetes cluster, network identity is fleeting. Containers are designed to be short-lived; when a pod is terminated, and a new one is created, a completely different IP address is assigned. This “ephemeral” nature makes traditional IP-based firewall rules obsolete almost instantly, leading to administrative overhead or, worse, massive security holes.
The integration of VMware vDefend and vSphere Kubernetes Service (VKS) solves this by decoupling security from the networking layer. Instead of relying on static IPs, vDefend uses Antrea CNI, the default CNI with VKS, to enforce context-aware policies based on logical metadata – such as labels applied to namespaces, services, and pods. Because the security policy is tied to the workload’s identity rather than its IP address, the protection follows the Pod automatically, even as it scales or is recreated on a different node. Furthermore, this enforcement occurs at the immediate point of origin—the Pod interface for containerized workloads and the vNIC for Virtual Machines within the Hypervisor. This ensures that security is applied at the ‘first hop,’ neutralizing threats before they ever traverse the physical or virtual network.
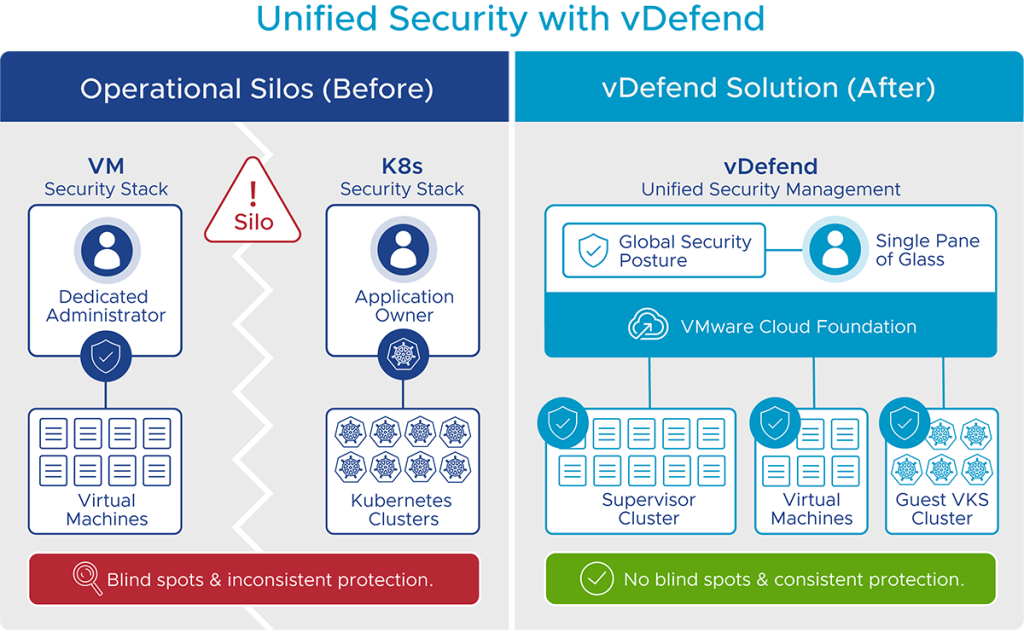
Unified Management: One Policy to Rule Them All
Operational silos, where separate security stacks have to be implemented for virtual machines and Kubernetes clusters, are a major hurdle in modern infrastructure, often leading to inconsistent protection and blind spots. vDefend addresses this by providing a unified security management solution for VMs and Kubernetes (VKS) workloads through a single pane of glass within VCF. This enables security administrators to define a global security posture that is consistently applied across the entire Supervisor cluster and all guest VKS clusters, without treating the VKS clusters as opaque entities.
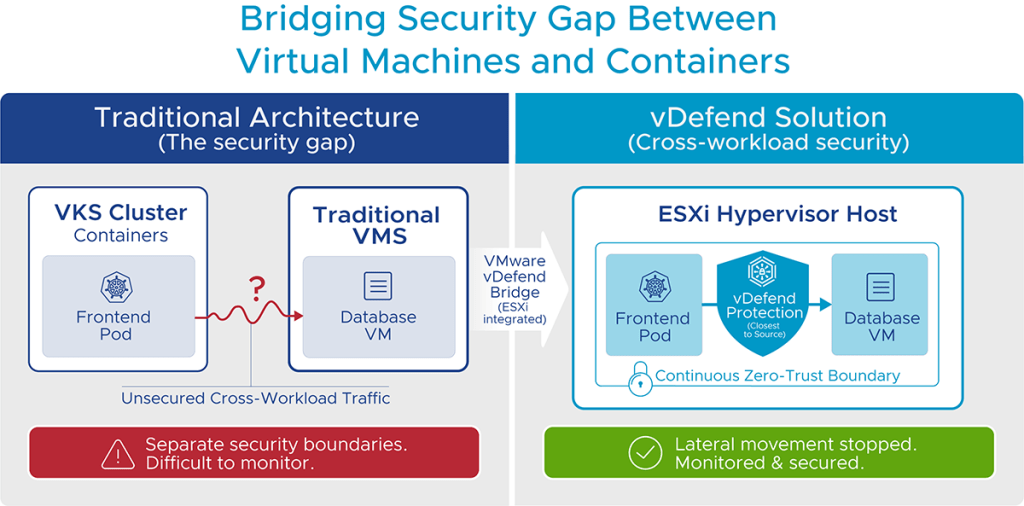
Bridging the Gap: Securing the “In-Between”
The most critical vulnerability in modern architecture often lies at the intersection of different workload types. A typical application might host its frontend in a containerized VKS pod while keeping its mission-critical database on a traditional virtual machine. Traditionally, these two worlds lived in separate security boundaries, making inter-workload traffic difficult to monitor and secure. VMware vDefend bridges this critical gap. Because it is natively integrated into the ESXi hypervisor, vDefend can inspect traffic closest to the source, as it moves between a container and a VM – even if they are on the same host. This cross-workload security ensures that the “mixed-mode” applications are protected by a continuous zero-trust boundary, stopping lateral movements regardless of whether the threat is hopping from a pod to a VM or vice versa.
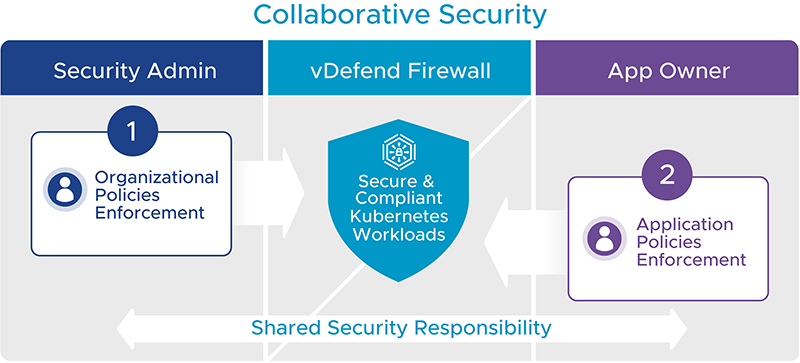
Control for Security Admins and Freedom for App Developers
In modern enterprises with Kubernetes workloads, security often becomes a shared responsibility between centralized security teams and application owners. While security teams typically define the organization’s overarching security model, application owners frequently control the security policies for their specific applications. While this ops model offers flexibility, it could create security gaps. vDefend addresses this by enabling security administrators and application owners to co-own container security policies through a central management view. Security administrators can control cluster-level firewall policies (ingress and egress traffic for a VKS cluster) to focus on environmental and infrastructure security. By utilizing vDefend’s distinct firewall categories, they can ensure these essential policies are always enforced first. Meanwhile, application owners retain complete autonomy to define application-tier Kubernetes networkPolicies without requiring explicit approval from security administrators. This collaborative approach ensures comprehensive protection across the board.
To truly understand the power of a unified security stack, it helps to look at how it handles real-world threats. By applying vDefend to VKS, administrators can move beyond broad “allow-all” rules and implement surgical precision in the security posture.
- Quarantining a Compromised Workload
One of the most important scenarios for a DevSecOps team is a “malicious-pod” – a container that has been compromised and is now attempting to scan the network for vulnerabilities and exfiltrate data. In a standard Kubernetes setup, this pod might have a “flat” path to every other service in the cluster. With vDefend firewall policies, you can execute a “Quarantine” strategy. By applying specific tags (e.g., quarantine = malicious) to the suspected pod, a high-precedence Emergency Category policy is instantly triggered. This policy overrides all other existing rules, immediately dropping all inbound and outbound traffic to the pod except for a secured connection to a “forensic pod” or a “jump host” for investigation. This drastically reduces the blast radius of the breach, stopping lateral movement before it starts.
- Hardening External Egress Traffic
In a Zero Trust environment, what goes out of your VKS cluster is just as important as what comes in. Many modern attacks, such as the Log4Shell exploit, rely on compromised workloads contacting malicious command-and-control systems. Protecting egress traffic in VKS is uniquely challenging because IPs are typically lost behind a generic Source Network Address Translation (SNAT) at the node. The solution is to leverage Antrea Egress to provide a stable, predictable identity for outbound traffic. By associating specific pods with an Egress IP, you can create granular vDefend firewall rules that allow only a specific production application to talk to an external database while blocking the rest of the cluster. This ensures that even if a workload is compromised, it cannot reach unauthorized external endpoints.
Future-Proofing with VCF and vDefend
By deeply integrating vDefend with VKS, the platform eliminates the traditional trade-off between developer agility and enterprise security.
Key Benefits for VCF Customers:
- Zero-Trust by Default: Organizations can now enforce a granular, Zero Trust model that covers the entire stack – from legacy virtual machines to ephemeral Kubernetes pods. This intrinsic security model stops ransomware and other sophisticated threats from moving laterally across your environment.
- Operational Simplicity: VCF and vDefend introduce a “single pane of glass” for policy management. Instead of juggling fragmented tools for container and VM security, administrators use a unified operational model that reduces the learning curve and eliminates manual configuration drift.
- Accelerated Time-to-Market: With self-service capabilities and automated policy orchestration, developers can spin up secured applications in minutes rather than months. Security is applied as soon as a workload is provisioned – security at the speed of apps, ensuring compliance from the very first packet without requiring tickets to multiple infrastructure teams.
- Deep Insights and Troubleshooting: The vDefend integration with VCF and VKS provides unparalleled insights into VM and container traffic flows. Features like Antrea Traceflow allow teams to synthetic-test their network paths, ensuring that every firewall rule functions as intended before an issue escalates.
Making VKS clusters vDefend Ready – video demo
Safeguarding your containerized workloads on VKS with vDefend shouldn’t be a complex hurdle. This video demonstrates just how simple it is to make the VKS cluster vDefend ready. By following the streamlined process, you can make your clusters vDefend-ready in minutes, unlocking powerful macro and microsegmentation capabilities. Whether you are managing existing deployments or spinning up new environments, this tutorial shows how remarkably easy it is to have your VKS cluster ready for vDefend.
Core insights from the video:
- Seamless Integration: Learn how the registration process acts as the “handshake” between your VKS cluster and vDefend
- Operational Simplicity: See firsthand that making a VKS cluster vDefend ready doesn’t require complex coding; it’s a straightforward workflow within the management console
- Automated Discovery: Discover how VKS namespaces, pods, and services are automatically recognized, enabling set-and-forget policies that scale as your cluster grows
Securing Modern Applications with VMware vDefend – video demo
Here is a video walkthrough of the simple steps for protecting modern applications deployed across a virtual machine environment and a VKS cluster. It showcases how robust security policies can be implemented in vDefend to prevent lateral movement between services in VKS clusters and also easily block unauthorized access to external systems from the VKS cluster.
Core insights from the video:
- Simplified Management: See how a single pane of glass with VKS and vDefend allows administrators to quickly and efficiently manage policies for both containerized workloads and virtual machine workloads
- Unified Security Policy: Understand how registering a VKS cluster allows you to apply consistent firewall rules across both traditional virtual machines and modern containerized workloads
- Egress Security: As mentioned above, Antrea Egress provides a stable, predictable identity for outbound traffic. This can be used to create granular vDefend firewall rules to allow only a specific service to communicate with an external database
vDefend is Key to a Secure and Agile Private Cloud
By adopting the models described above, VCF operators who deploy vDefend are building resilient, scalable, and automated security foundations. As applications continue to evolve into complex webs of containers and VMs, having a unified security layer is no longer just a “best practice” – it is the key to maintaining a secure and agile private cloud.
Further Reading:
Check out the detailed Securing vSphere Supervisor and VKS with vDefend reference design, which serves as both an architectural blueprint and a practical implementation handbook for using VMware vDefend security solutions. It offers essential design insights and security recommendations to enhance the protection of vSphere Supervisor and the mixed-form-factor workloads running on it: Virtual Machines, vSphere Pods, and VKS.