The Dark Web is part of the internet that provides anonymity to its uses. Unfortunately, this anonymity creates a setting for buyers and sellers to trade their content. In cybersecurity, this is where credit cards, medical records, personal information, user credentials, and more grievous data sets are sold. Cryptocurrency is generally the method of payment, again, to preserve anonymity.
Think of the Dark Web as a shopping center or mall. The ground floor is where anyone can browse and shop. The stores range from department stores to thrift shops which no specialist products and services. On the next level of the mall are more specialist stores where you must be a member before entering. This membership is based on trust, trade, and credibility. Access is restrictive but possible. On the next level are elite and premium stores. These cannot be accessed via a lift or escalator, and admission is by invitation only.
The point is, the dark web is not readily accessible to the average internet user and monitoring the goings on is not a one-person job. This is why businesses turn to special services to monitor the dark web for their own sensitive information.
What are Dark Web Scanning Services?
The number of dark web monitoring services has grown exponentially over the past few years, but are they worth it? What are the realities of this service and why do some organizations get a false sense of security from it?
Numerous organizations are presently offering Dark Web monitoring services, yet there is still a broad misconception about how they work or whether they work at all. Types of dark web monitoring include:
- Scanning services – scanning hundreds of thousands of hidden websites each day looking for your organization’s information.
- Trading services – where they will trade on your behalf, to validate information, get insights, or purchase your data. For example, banks may purchase credit cards issued by them to cancel them.
- Collaboration services – chatting on forums around attack opportunities, zero-day exploits, and intelligence sharing.
Now that you understand the different services, does this mean they are worth your time and money? Here is what you need to know.
How Effective are Dark Web Scanning Services?
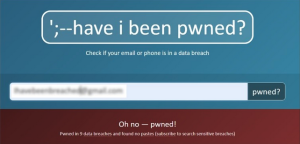
Despite the exquisite marketing campaigns of many providers, you need to know that none of them can scan the entirety of the Dark Web, which is an impossible task. The reality is that they will check the most publicly available databases (with 8+ billion entries), which typically holds old data, commonly an accumulation of previous breach data sets. It is less likely that they will scan the forums that are only accessible by trusted members and highly unlikely they perform a deep web scan where peer-to-peer trading occurs. So, if you plan to use them, keep in mind they will monitor and report on publicly available information; they do not delete it.
 Typically, they will provide a portal to access helpful management tools to customize scan criteria and include reporting. These interfaces are handy, but at the end of the day, they only provide insights on what they scan and not the whole Dark Web.
Typically, they will provide a portal to access helpful management tools to customize scan criteria and include reporting. These interfaces are handy, but at the end of the day, they only provide insights on what they scan and not the whole Dark Web.
When something winds up on an underground site, options are limited to remove it. Some dark web sellers may promise to delete it once you pay — but can you really trust them?
The reality is they won’t. After all, you are negotiating with dodgy individuals with compromised ideals, whose motive is profit and don’t care for the harm they facilitate.
Announcement: VMware Wins Global Infosec Awards at RSA 2022
Should You Rely on Dark Web Trading Services?
Invariably this is where the real action is. I have been fortunate to work with individuals who possess the knowledge and have the established networks to perform this service. In my experience, the number of individuals who can operate in this area is minimal compared to the generalists.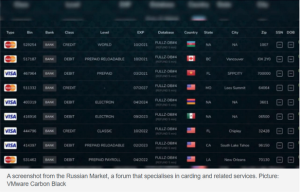
Typically, the individuals with this skill are repentant hackers, law enforcement, military, and intelligence officers. The challenge I have, and this is my value system here, is that if a person has gained the trust of the inner sanctum of the illicit trading floors, they have done so by questionable actions themselves. And because of this, I struggle to believe they have the underlying integrity required. I have seen cases where trading analysts act as double agents, where they have swapped sides depending on who is paying the most, and issues where they work as a buyer and seller on the same transaction.
5 Best Practices When Considering Dark Web Monitoring Services
- Qualify Hard
Ask lots of questions to ascertain whether they are a tech firm providing an elaborate search function or do they have operatives inside these forums. Ask them how many search analysts they have, how many languages are spoken in their team, the countries where the analysts are located, how do they source insights, have they registered their services with police and intelligence teams, and can they show you examples of the forums they are participating in.
- Test
Run a 90-day trial rather than a full subscription – so that you can test the integrity of their capabilities. If they are doing an automated search only and not a manual analyst-driven effort, you may want to check other options.
- Legal Protection
Ensure you have legal protection in place, including provisions for inappropriate actions.
- Be Smart
Never give the agents sensitive PII to search on, such as your birth date, bank account details, secret keys, etc. Accept the notion that what you share may be sold.
- Use Open-Source Intelligence (OSINT) Tools first
There are many OSINT tools that you can use straight up to provide invaluable insights. Start with these, and then consider if you have any gaps in your intelligence.
Learn More: Why CISO’s Should Invest More Inside Their Infrastructure
Is Dark Web Monitoring Worth It?
So, to answer the question, is it worth it?
The answer is a partial yes, so long as you have realistic expectations, have tested their capabilities, and do not buy into the hype around surveillance services. Dark web monitoring would be in my cyber program but low on my priority list. It’s better to invest in proactive solutions rather than weaker reactive ones such as this. If you’ve implemented a Zero-Trust security architecture, extended detection and response (XDR), multi-cloud protection, and DLP, you are in a better position to start with.
Keep in mind something I learned many years ago when I delivered my first dark web monitoring report at a Board Meeting; they asked, “what do you expect me to do about this?”. I quickly learned that any reporting method must have an accompanying action because, without an action, the report is just hype.
Before you invest serious resources in this service, I suggest you focus on making your data set as dark web dull as possible, such as:
- Delete non-essential data from your network – it amazes me how much unnecessary data we store, such as old resumes, that we need once and no longer need
- Seriously challenge data sharing with 3rd parties and ensure they have good security in place
- Encrypt sensitive data at rest and in transit – PII, credit cards, medical information, etc.
- Store credit cards off your network on PCI accredited servers
- Have business processes to quickly identify fraudulent activity – such as overseas transactions on gift cards/credit cards, dormant cards, chargebacks, etc.
- Focus on effective user awareness education, not just training. Personally, sit with your business teams and coach them on good practices, and establish cyber champions in the business.
I wish you every success as you improve your cyber capabilities.







