In any given attack campaign, bad actors have a specific goal in mind. This goal may involve accessing a developer’s machine and stealing a project’s source code, sifting through a particular executive’s emails, or exfiltrating customer data from a server that’s responsible for hosting payment card information. All they need to do is compromise the system that has what they want. It’s just that easy.
Or is it?
In reality, it’s a little more complicated than that. When attackers compromise an asset in a network, that device usually is not their ultimate destination. To accomplish their goal, bad actors are likely to break into a low-level web server, email account, employee endpoint device, or some other starting location. They’ll then move laterally from this initial compromise through the network to reach their intended target. The initial compromise seldom causes severe damage. Thinking about this another way: if security teams can detect the lateral movement before the attackers reach their intended targets, they can prevent the attacker from successfully completing the mission.
But what exactly is lateral movement, and how does it work? In this blog, we’ll look at some of the most common types of lateral movement and identify ways by which we can detect and defend against this step in an attack.
What is Lateral Movement?
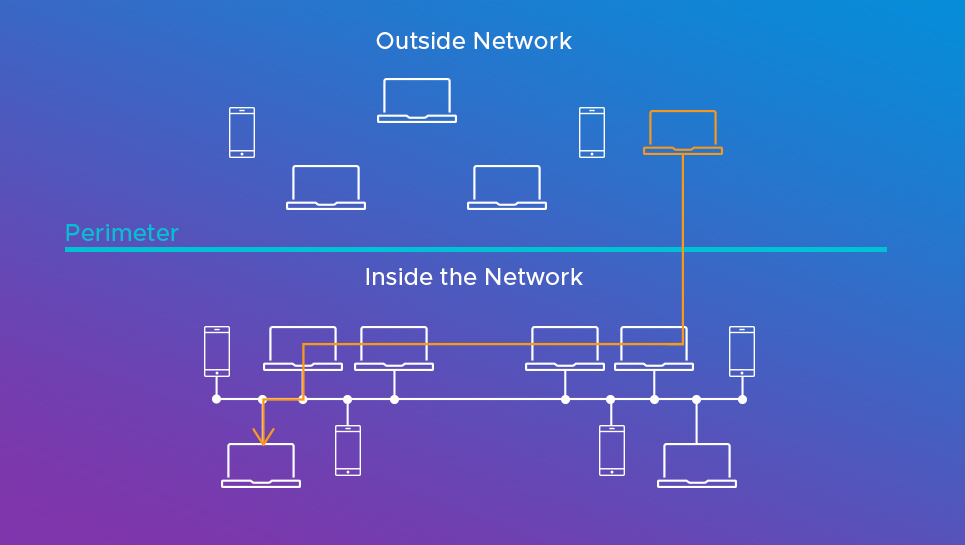
Lateral movement is when an attacker compromises or gains control of one asset within a network and then moves on from that device to others within the same network. Let me draw you a picture to help clarify what’s going on here. In any network, you can represent the perimeter with a horizontal line. The top half represents what’s outside the network, while what lies below the line represents what’s inside. For an attacker to get inside the network, they must move vertically — that is, from outside to inside (sometimes called north-south traffic). But once they’ve established a foothold, they can then move laterally (or horizontally, sometimes called east-west traffic) within the network to reach their objective.
Overall, there are common ways by which a threat actor moves laterally. In one approach, the attacker uses tools designed to internally scan the network to gain information on other machines they may want to move to. Many of these enumeration tools do things like scanning for open ports that are listening and identifying machines that are suffering from unpatched vulnerabilities. Once the attacker has found a suitable target, they can take advantage of these weaknesses to move laterally to another asset.
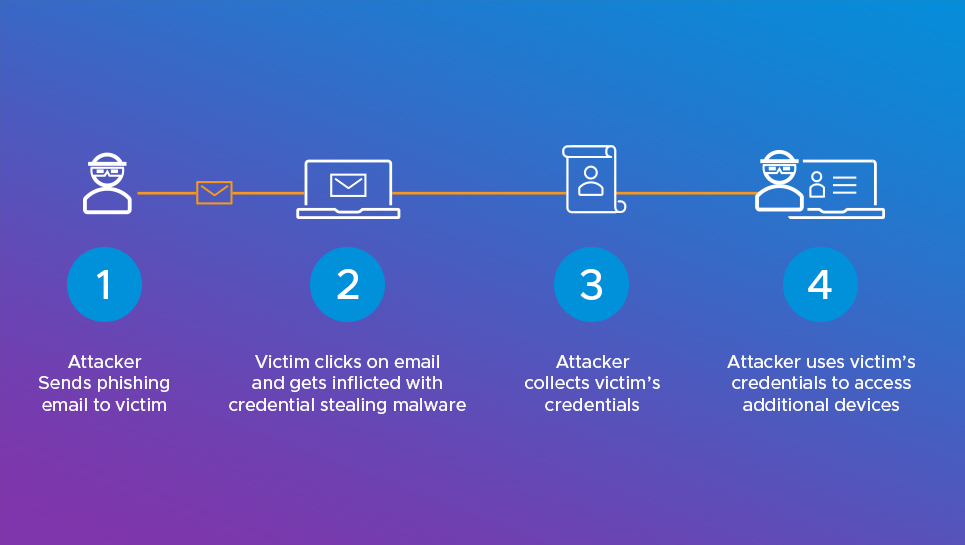
Another method of lateral movement exploits stolen credentials. In this type of attack, the intruder might use a phishing email to infect a machine that interfaces with a particular server. The attacker can then use his access to scrape for passwords via a keylogger or password-stealing tool like Mimikaz. Next, they can use whatever credentials they were able to obtain to impersonate the victimized user and log into another machine. Once they’ve established access on that computer, they can then repeat the tactic by looking for additional shares, credentials, or privileges that they can exploit and, in turn, use along the path towards establishing a remote connection to the target device.
Defending Against Lateral Movement
It’s worth saying that lateral movement often manifests as anomalous network activity. It’s suspicious, for example, when a machine that talks regularly with only a select few computers begins scanning the entire network. The same is true if that machine attempts to connect to open ports, interact with credential services with which it doesn’t ordinarily maintain contact, or employ a username it’s never used before. The list goes on and on. What matters is that the computer is doing something out of the ordinary. Maybe there’s a legitimate reason for the activity, but maybe there’s not.
Examples like the ones above can give organizations a chance to detect lateral movement. They can turn to Active Directory, for example, to analyze log files for suspicious connections. Alternatively, they can use an endpoint detection and response (EDR) tool to detect if someone launches malicious code on a protected IT asset.
But these defenses aren’t foolproof. Security teams who rely on logs limit the scope of their defensive posture, for example, because logs are limited to particular apps and a small number of scenarios. Infosec professionals might decide to monitor Active Directory for credential theft, but attackers might not leverage this directory service to move laterally. This means that any and all malicious actions that don’t use Active Directory may go undetected. Beyond that, skilled attackers know the types of protocols that security personnel tend to monitor. They can use this knowledge to mold their attack campaigns so that they stand a better chance of flying under the radar, or to give themselves enough time to successfully execute their attack before anyone notices.
The NSX Network Detection and Response Advantage
It’s simply not enough for organizations to look for lateral movement using logs or an EDR tool. Instead, they need to turn their attention to the network. Doing so will allow organizations to see all network traffic, establish a baseline of normal network activity for each user and device, and monitor for unusual actions that could be indicative of malicious lateral movement. Known as anomaly detection, this task is more comprehensive and often easier than instrumenting every service and examining every log file for anomalies.
The problem with anomaly detection is that many of these irregularities are benign. What’s needed to separate malicious lateral movement from benign network anomalies is an understanding of what malicious behavior looks like. That’s where NSX Network Detection and Response comes in. NSX Network Detection and Response understands threats and knows what malicious behavior looks like. Our automated analysis systems monitor, analyze, and protect against millions of threats every day. Using that threat behavior information, our machine learning system can automatically build powerful classifiers that identify, with very high accuracy, those network anomalies that exhibit malicious behaviors, leaving behind benign network anomalies that otherwise generate false positives.
Up your organization’s game against lateral movement.







