In Part 1 of this blog series, we introduced a new feature of VMware Horizon 7 called True SSO (Single Sign-On).
In this blog post, we will cover the steps required to implement True SSO in a lab environment. This won’t cover subjects such as High Availability or complex domain trust scenarios (they will come in a future blog post), but should be enough to get you up and running so you familiarize yourself with the True SSO capabilities and system architecture.
Below is a diagram providing an overview of what we would like to have set up by the end of this blog post:

The environment can be built out in two distinct phases:
(A) In the lab environment we will have a Horizon 7 View environment comprised of:
- Windows Server 2012 R2 Domain Controller (Microsoft component)
- Windows Server 2012 R2 with Horizon 7 Connection Server (CS)
- Windows Desktop (can be any Windows 7/8.1/10/2008 R2/2012 R2) with Horizon 7 Agent
- VMware Identity Manager (vIDM) 2.6
- vIDM will be paired to the Horizon 7 CS
- SAML authentication in the Horizon 7 CS will be configured
- RSA SecurID or RADIUS authentication enabled on vIDM
(B) For True SSO we will add:
- Windows Server 2012 R2 Certification Authority (CA) (Microsoft component)
- Windows Server 2012 R2 with Horizon 7 Enrollment Server (ES)
 Note: You could also set this up using Windows Server 2008 R2 CA and AD (Active Directory) infrastructure. Some of the screens/steps are slightly different, but this is supported.
Note: You could also set this up using Windows Server 2008 R2 CA and AD (Active Directory) infrastructure. Some of the screens/steps are slightly different, but this is supported.
Once (A) is built out, you will have a fully functioning Horizon View environment, which allows desktops to be launched from vIDM. (B) adds the additional components to enable True SSO.
With the above in mind, we will step through the following checklist:
- Prerequisites: The infrastructure described in (A) is a standard Horizon View deployment and can be performed by following any Horizon deployment guide.
- Infrastructure Setup: We will discuss setting up and configuring a CA, setting up a Horizon ES and then pairing the ES to the Horizon CS.
- Configuration: We will discuss additional configuration steps in vIDM and how to configure True SSO on the CS.
- Testing: We will finally try out True SSO and confirm that it is working.
Prerequisites
So, the first step is to get a Horizon environment up and running. This can just have a single connection server, and for this lab environment you don’t need to worry about configuring for external access, so you can skip adding the Access Point (or security server).
Once that is set up, please try logging on to a Horizon desktop using the Horizon client and confirm that you can successfully log in (using AD credentials) to the desktop.
Next, add vIDM and configure the SAML pairing between Horizon and vIDM. (See these YouTube videos if you need help: Integrating Horizon View and Horizon Workspace, Part One and Configuring Horizon Workspace to integrate with Horizon View, Part Two.)
Ideally, at this stage, configure vIDM to use RADIUS or RSA SecurID so that initial logon does not prompt for passwords.
From here, verify that you can log into vIDM and see your desktop entitlements. Clicking them should launch Horizon (which if you have configured RADIUS/RSA SecurID will then prompt you for your AD credentials). Verify that you are logged into your Windows desktop.
Once that’s up and running, you are ready to set up True SSO!
Infrastructure Setup
In this section we will:
- Set up a Windows Server 2012 R2 CA. The CA will issue certificates on behalf of the users, and those certificates will be used to log the users in to their allocated desktops. After setting up the CA we will do some additional configuration, such as setting up certificate templates, and run some configuration commands required for True SSO.
- Set up a Windows Server 2012 R2 environment, install the ES and deploy certificates required for True SSO. Horizon CS will ask the ES to issue certificates on behalf of users. The ES will generate the requested certificate on behalf of the requested user via the CA and return it to the Horizon CS.
Note: The steps below are detailed for Windows Server 2012 R2. Very similar steps can be followed on Windows Server 2008 R2 if you prefer to test with that.
Install & Configure Windows Server 2012 R2 CA
The following are standard steps to set up a Microsoft CA. They are detailed here in a simple form suitable for use in a lab environment, but for a real production system it is recommended that you follow industry best practice for CA configuration.
How to install CA via Server Manager wizard
On Server Manager, follow these 20 steps:
- On Server Manager Dashboard, click “Add Roles and Features” to open the wizard and click “Next”
- Select Installation Type: select “Role-based or feature-based installation” and click “Next”
- Server Selection: leave defaults and click “Next”
- Server Roles:
- Select “Active Directory Certificate Services”
- A dialog box will pop up. Select “Include management tool” (if applicable) and press “Add Features”
- Click “Next”
- Features: click “Next”
- AD CS: click “Next”
- Role Services: select “Certification Authority” and click “Next”
- Confirmation: select “Restart the destination server automatically is required” and press “Install”
- Installation Progress: when completed, it will provide a URL link to configure the newly installed CA as “Configure Active Directory Certificate Services” on the destination server
- Clink on the configuration link and the configuration wizard starts
- Credentials: Provide user credentials from Enterprise Admin group and click “Next”
- Role Services: select CA and click “Next”
- Setup Type: select Enterprise CA and click “Next”
- CA Type: select Root or Subordinate CA as appropriate (for our example we will presume it’s a Root CA) and click “Next”
- Private Key: select “Create a new private key” and click “Next”
- Cryptography:
- Cryptographic Provider: RSA#Microsoft Software Key Storage Provider
- Key Length: 4096 (or another length if you prefer)
- Hash Algorithm: SHA256 (or another SHA algorithm if you prefer)
- CA Name: configure as preferred or accept defaults and click “Next”
- Validity Period: configure as preferred and click “Next”
- Certificate Database: click “Next”
- Confirmation: review and click “Configure”
If you need further guidance about setting up a CA, please check out the standard Microsoft technical references: Active Directory Certificate Services Step-by-Step Guide and Install a Root Certification Authority.
True SSO: Setup Certificate Template on CA
In this step, we will configure the certificate template on the CA. The certificate template defines what the certificates the CA generates will “look like.”
Step 1. We will create a new Universal Security Group. This allows us to have a single Security Group to which we can assign the permissions required for issuing Certificates on behalf of users. And all the computers where VMware ESs are installed can inherit those permissions by becoming a member of this group.
- On the Domain Controller we setup a new Universal Security Group called “TrueSso Enrollment Servers.”

- Then we add the computer where the ES will be installed to that group.

- Restart the computer(s) where the ES(s) will be installed for the changes to take effect.
Step 2. Set up Certificate template.
- On the CA select Control Panel > Administrative Tools > Certificate Authority.
- Expand the local CA name and select “Certificate Templates,” right click and select “Manage.”

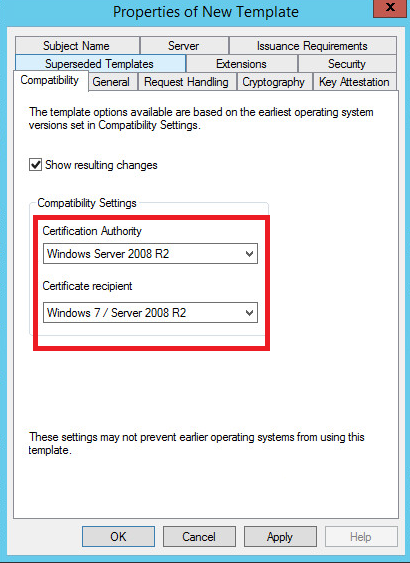
- From Certificate Templates Console, find the “Smartcard Logon” template and select “Duplicate Template” option from the right-click menu option.

- Adjust the settings of various properties of the new template as marked in screenshot.
Step 3. Issue template for True SSO.
- Right click “Certificate Templates” > New > Certificate Template to Issue.

- Select “TrueSsoTemplate” from the “Enable Certificate Templates” dialog and press “OK.”
Step 4. Issue Enrollment Agent template.
- Right click “Certificate Templates” > New > Certificate Template to Issue.
- Select “Enrollment Agent (Computer)” from the “Enable Certificate Templates” dialog and press “OK.”
Note: We should verify that the “Enrollment Agent (Computer)” template has the same security settings as we specified when creating “TrueSsoTemplate” (ie. TrueSso Enrollment Servers Security Group is added and has Read/Enroll permissions).
Step 5. CA: from the command prompt run the following commands:
- Configure CA for non-persistent certificate processing
- “certutil –setreg DBFlags +DBFLAGS_ENABLEVOLATILEREQUESTS”
- Configure CA to ignore offline CRL errors
- “certutil –setreg ca\CRLFlags +CRLF_REVCHECK_IGNORE_OFFLINE”
- Restart the CA service. From the command prompt run:
- net stop certsvc
- net start certsvc
At this stage, the CA should be setup and configured with a certificate template suitable for use with True SSO.
Enrollment Server
The ES is a new component of Horizon 7. It needs to be installed on a Windows Server 2008 R2 or 2012 R2 machine, with a minimum of 4GB memory.
Step 1. Install. Download the Horizon CS installer and install on a Windows 2008 R2 or 2012 R2 Server VM. While running the installer we select “Enrollment Server” from the server types available.

Step 2. Certificate deployment (1/2) – Enrollment Agent (Computer). By deploying the Enrollment Agent (Computer) certificate onto this server, we are authorizing this ES to act as an Enrollment Agent and generate Certificates on behalf of users. To do this:
- Open the Microsoft Management Console (MMC) and select Add/Remove Snap-in > Certificates > Computer account > OK.
- Request the “Enrollment Agent (computer)” certificate and import to MyStore (Personal).


Step 3. Certificate deployment (2/2) – Enrollment Service Client Certificate. By deploying the Enrollment Service Client Certificate from the CS, we are pairing the Horizon CS with the Horizon ES. Without the trust, the ES will reject any connection requests and, therefore, will not generate any certificates. Enrollment Service Client Certificate is automatically generated on the CS machine when the Horizon CS service starts and is stored in a custom container (VMware Horizon View Certificates\Certificates) in the Windows Certificate Store.
On the Horizon CS machine:
- Open the MMC and select Add/Remove Snap-in > Certificates > Computer account > OK.
- Browse to VMware Horizon View Certificates\Certificates, identify the Certificate with Friendly Name “ec” and export it to a file without the private key.

- Next, we go to the machine where we installed the ES. We import the above exported Enrollment Service Client Certificate to Windows Certificate Store of Local Machine. We place it in a custom container called: “VMware Horizon View Enrollment Server Trusted Roots.”

At this stage, the ES is now trusted by the CA to request certificates, and it trusts the CS to generate requests for certificate generation.
Configuration
In this section we will:
- Perform additional configurations on vIDM required for True SSO. The configuration includes suppressing password prompts when vIDM does not have the AD credentials for the user.
- Configure True SSO on the Horizon CS. True SSO will be configured for a specified domain such that any users launching desktops or apps from vIDM will log in using True SSO.
- Check True SSO status on the Dashboard. Once True SSO is properly configured, we will verify its status on the Horizon CS admin dashboard.
1. vIDM Configurations
For True SSO to work with vIDM and Horizon 7, we need to log into the vIDM administration page of the View Pools and enable “Supress Password Popup.”

Without doing this, vIDM will prompt the user for a password when launching a Horizon desktop or app if it doesn’t already have a password cached. For True SSO we do not need to cache passwords or request this, hence the option to suppress the password popup.
2. Configure True SSO on the Horizon CS
We will set up Horizon CS to use True SSO for a certain domain by using a command line tool called “vdmUtil.”
vdmUtil is located in the Horizon CS folder. Typically it can be found here:
%PROGRAMFILES%\VMware\VMware View\Server\tools\bin
Launch a command console, and then execute the following commands in sequence:
Step 1. Add the VMware ES to the environment. For this you need to know the Fully Qualified Domain Name (FQDN) of the machine where the VMware ES is installed.
By adding the ES to the environment, we are able to query the ES about the domain and relevant True SSO info (eg. what templates are available, what’s the Common Name of the CA, etc.) that would be useful to configure it.
Syntax:
vdmUtil –authAs <username> –authDomain <netbios domain name> –authPassword <password> –truesso –environment –add –enrollmentServer <FQDN of Enrollment Server Machine>
Example:
vdmUtil –authAs administrator –authDomain TESTDOM –authPassword password –truesso –environment –add –enrollmentServer enrollServer.testdom.company.int
Step 2. List info from the ES.
Here we will find out detailed info about identify various components of the environment which will be useful for configuring True SSO.
Syntax:
vdmUtil –authAs <username> –authDomain <netbios domain name> –authPassword <password> –truesso –environment –list –enrollmentServer <FQDN of Enrollment Server Machine> –domain <FQDN of Domain>
Example:
vdmUtil –authAs administrator –authDomain TESTDOM –authPassword password –truesso –environment –list –enrollmentServer enrollServer.testdom.company.int –domain testdom.company.int
Output (will display something like the following info):
Enrollment server: enrollServer.testdom.company.int
Domain: testdom.company.int
Forest:
Name: testdom.company.int
Enrollment CertState: VALID
Template(s):
Name: TrueSsoTemplate
Minimum key length: 2048
Hash algorithm: SHA256
Certificate Authority(s):
Name: testdom-rootca
Step 3. With the above info we create a Connector for True SSO.
A True SSO Connector is a configuration set where we specify details like ES(s), CA(s) and a Certificate Template to use for a certain Domain. When a Horizon CS gets a request to launch a desktop for an AD user, it will look up True SSO Connector for the domain the user belongs to and will use the components as specified to obtain a Certificate on behalf of the user.
Syntax:
vdmUtil –authAs <username> –authDomain <netbios domain name> –authPassword <password> –truesso –create –connector –domain <FQDN of domain> –template <name> –primaryEnrollmentServer <FQDN of Enrollment Server> –certificateServer <Common name of CA> –mode enabled
Example:
vdmUtil –authAs administrator –authDomain TESTDOM –authPassword password –truesso –create –connector –domain testdom.company.int –template TrueSsoTemplate –primaryEnrollmentServer enrollServer.testdom.company.int –certificateServer testdom-rootca –mode enabled
Step 4. List all SAML Authenticators available in the Horizon View environment.
A SAML Authenticator contains the trust and metadata exchange between Horizon View and vIDM. To use True SSO, we need to identify the correct SAML Authenticator and enable True SSO.
Syntax:
vdmUtil –authAs <username> –authDomain <FQDN of domain> –authPassword <password> –truesso –list –authenticator
Example:
vdmUtil –authAs administrator –authDomain TESTDOM –authPassword password –truesso –list –authenticator
Output (displays something similar to the following info):
Authenticator(s) found: 1
Name: vidm.testdom.company.int
TrueSSO Mode: DISABLED
Step 5. Enable True SSO for the SAML Authenticator.
Syntax:
vdmUtil –authAs <username> –authDomain <netbios domain name> –authPassword <password> –truesso –authenticator –edit –name <authenticator name> –truessoMode ENABLED
Example:
vdmUtil –authAs administrator –authDomain TESTDOM –authPassword password –truesso –authenticator –edit –name vidm.testdom.company.int –truessoMode ENABLED
3. Check Status on Dashboard
Assuming we have successfully completed the steps above, True SSO should now be correctly configured for domain “testdom.company.int.” To verify the state of True SSO, we can now go to the admin page of the Horizon CS and check the Dashboard.
We should see something like this (the dialog on the right is seen when you double click on “testdom.company.int” beneath True SSO menu item):

Testing
Now we can launch a web browser and connect to vIDM. Once authenticated (via RADIUS or RSA SecurID), we should be able to see all entitled desktops and apps.
We can launch any desktop or app with a click on the icons. The user should not be prompted for AD credentials and will be logged into the desktop or app with an interactive session. If you reached this stage, True SSO is working! We can now check the logs on the desktop where the user logged in to verify that True SSO worked as expected.
After logon is completed we can open the debug logs for Horizon View Agent. This will typically be:
%PROGRAM_DATA%\VMware\VDM\logs\debug-<date>-<pid>.txt
Filter the files to show the latest modified and open the latest debug log file. Here we should be able to spot the following log lines:


Conclusion
This concludes our blog post where we walked through the steps in setting up True SSO with Horizon View in a lab environment.
Now that we are familiar with the basic setup of True SSO, we will discuss how to architect a True SSO environment for production use in the next blog post. We will also discuss some advanced configurations like High Availability and complex domain support for True SSO.