I’m very excited to announce today a new solution called, VMware Identity Manager, a unique identity as a service (IDaaS) solution for the mobile-cloud.
The Identity Management market is heating up again as Enterprises make the gradual shift toward cloud-first strategies to transform IT operations. On the surface, the reasons are obvious. Any employee of a company larger than about 20 people feels the pain of trying to get work done when they aren’t sitting in front of a domain joined computer in the office, and even then, the occasional need to access an HR app, and likely a CRM app still requires yet another password.
That said, the average employee (and help desk) has been fighting passwords for 20 years, so why now?
I’d love to say that it is because IT and lines of business have finally realized the plight of the working class and are investing to make convenience and productivity job #1, but while I do think any CIO wants to be seen as getting out of the dark ages of user experience, it’s not what drives spending priorities. So then what is it?
…Security
The transformation from a client-server, perimeter-based model of IT to the mobile cloud is inevitable. The economics and ability to differentiate and compete REQUIRES taking dependencies outside of the firewall. At the same time, threats have changed. Even 5 years ago a hacker was a mischievous “kid” showing off to friends. Perimeter security and antivirus could be thrown at the problem and the illusion of security was upheld. That has changed. Malicious and directed attacks are no longer the realm of paranoid computer scientists, they happen… and not just to banks, but to retailers, manufacturers, transportation and entertainment companies and the risks to business have become too high to ignore.
Identity Federation, an Old Idea Now More Important Than Ever
In the client-server world, there have been more or less effective ways to handle passwords related to internal applications with their own user directories. The principle issue was the cost of helpdesk tickets in performing password resets, so password form fill management systems became commonplace in organizations large enough to justify the cost and complexity. These systems didn’t work for all applications, but did pay for themselves in reducing ticket costs, let alone the productivity gained by employees when their sticky note of passwords fell off or they were stranded in a hotel room without their crib sheet in the desk drawer. Still, the business risk that went along with client-server authentication wasn’t so much about external attack, it was merely enforcing internal role-based access to limit fraud and enforce compliance controls. The real external security was about the physical door to the office, and access to the physical network from an authorized, domain joined, and image managed computer.
In a mobile cloud world, there are new challenges. Perimeter security is still important for legacy systems, but the “trust” afforded by physical networks, VPNs, badges, and domain-joined devices no longer pertain to a growing list of business functions that live in the mobile cloud. Each of these new business services carry another set of identities for our users requiring another set of credentials and authentications access from both browsers and directly from mobile apps.

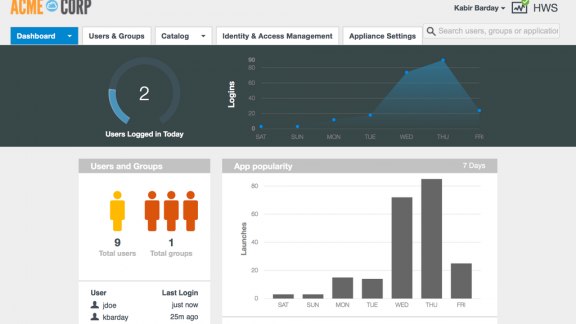
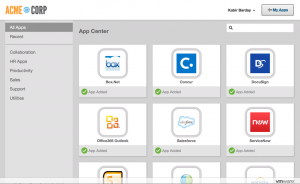
At it’s core, VMware Identity Manager enables mobile cloud identity federation so that IT can continue to manage the 1:many relationship between a user’s corporate identity and all the other identities they carry across the cloud in both SaaS and Mobile Apps. When a user arrives, or more importantly leaves a job, access can be granted or revoked immediately while eliminating the manual error-prone ticket processes typically used to provision and de-provision users.
Human Engineering – Improving Authentication

Passwords have been maligned as a security mechanism for as long as they have been in use. They presume a “shared secret” that only one person knows and remembers which presents the crux of the problem, humans. If we listen to IT, we have unique, long, randomly selected strong of characters that is impossible to actually remember and even more impossible to type with thumbs on a mobile device. This of course leads to writing down, caching, and or constantly resetting passwords that weaken the shared secret and add friction to the end user.
The combination of VMware Identity Manager and AirWatch® leverage the shift in device management to create device identities that we can bind to users so that possession of an unlocked device can be used as a seamless factor of authentication not unlike the experience consumers already enjoy with their mobile devices. More importantly, because people have such a strong connection with their personal devices, it is less likely that they will lose control of them, and when they do, are more likely to report them stolen and/or initiate their own remote wipe to safeguard their personal information, as well as corporate information.
Modern device OS platforms such as Android for Work and iOS also enable device management extensions through AirWatch Management for stronger authentication like biometrics and the ability to manage timeouts for further security.
In fact, VMware Identity Manager with AirWatch Adaptive Access can create an industry first single-touch experience that can authenticate a user against the enterprise directory without prompting for yet another password across both iOS and Android device platforms – without requiring code changes to the app. The elimination of app wrapping or modification requirements for SSO to mobile apps not only cuts down on testing, but assures users can take advantage of the latest application updates, complete with their own security updates.
Conditional Access and managing data at rest
If you asked me even a few years ago years ago where I thought end user computing was going, I would have spun a great story about the power of HTML5, rich and responsive web applications, and the ability to carry around nothing more than a browser with a keyboard and a screen to get nearly anything done. All of the applications and the data were going to live in a datacenter, so our security problems were solved. I could pick up any generic device, login through a secure proxy and know that the actual data I was using and generating would stay safe in the confines of a glass room.
Then I bought my first iPhone, iPad and then really started relying on them for daily productivity.
I quickly found that the network was not as ubiquitous as I had hoped, even in densely populated areas. The more I could be connected, the more I demanded it, and the more I appreciated applications that could hold state and sync with cloud services so that I could maintain an illusion of being connected, but rarely be inconvenienced by outages.
So where does this leave us in 2015? If I want to run Salesforce.com reports on sales opportunities in my office, I only need a browser and no data remains on my laptop. If I want to run the same report from my mobile device, information is pushed and stored on my device. See the dilemma?
That’s where conditional access comes in. VMware Identity Manager leads the industry with unique conditional access controls that allow administrators to set policies on whether a device is managed or unmanaged. If an application stores sensitive data, it should be under management so that information can be wiped if lost, stolen or otherwise compromised.
However, not all applications are as sensitive as others. In the demonstration available from our site, you can see scenario where an application like Webex or Concur can be access without management, and not requiring a password entry. If the same user then wants access to the Salesforce1 app, they must then enroll the device under management so that the application state can be protected.
VMware Identity Manager is now available as part of the Blue and Yellow Management Suites and will soon as a standalone offering as well. The easiest way to experience VMware Identity Manager is to apply for an AirWatch trial where the complete system can be provisioned for you in the cloud so you can tour the solution for yourself. More information can be found at http://www.vmware.com/products/identity-manager.
If you’d like to learn more about VMware’s Business Mobility strategy, register for our online event scheduled for tomorrow, Tuesday, June 16 at 9 am PT/12 pm ET.
VMware, VMware Identity Manager, and AirWatch are registered trademarks or trademarks of VMware, Inc. or its subsidiaries in the United States and other jurisdictions.