by: VMware Incident Response Specialist Hemant Kumar
With the ever-growing sophistication of ransomware and attack techniques, there’s always a need to maintain software defenses and tune our security products on a regular basis. Software development is the process of developing software through successive phases in an orderly way. The process typically includes identifying what’s required and providing detailed software and design specifications, preparing requirements and objectives, writing the code, software programming, and testing to confirm that what’s developed meets the objectives.
An example of how software development can help VMware IT meet its requirements and also offer new products is the development of our “RoadBlock” tool, which protects us from any kind of ransomware attack.
The VMware security incident response team handles multiple types of cyber incidents, the bulk of which involves determining whether a device has been compromised, with or without the use of malware. The team then must stop the suspected compromised device from carrying out further cyberattacks. This requires the ability to detect malware that was able to bypass existing security products such as antiviruses.
In 2019, there was a sudden spike in the news that various organizations around the world were being affected by ransomware that would lock their data and then demand ransom. Ransomware is a type of malware that prohibits users from accessing their system or files and requires a ransom payment to regain access, often resulting in data loss, downtime, lost productivity, and reputational harm. The situation has grown worse, with the latest prediction that global ransomware damage costs will reach $20 billion in 2021.
This is why the idea of developing a new kind of ransomware protection software gained momentum in the VMware IT Information Security operations team. Additionally, because many of our existing cybersecurity products were failing to detect new variants of ransomware, there was a strong motivating factor to invest time in developing our Roadblock product.
The idea was to develop software that can detect any kind of ransomware on a device and disinfect the live system instantly, without any data loss. This was not an easy undertaking due to the growing sophistication of ransomware that could evade multiple cybersecurity defenses. However, since our team often investigates suspicious malware incidents using cyber (network, disk, memory) forensic skills to detect malware with high accuracy where other cybersecurity products failed, we wanted to test our skills in solving the ransomware problem.
The first step was to design how ransomware protection software defenses should work. Our plan came from war movies, in which a country would protect its citizens using multiple lines of security, with each line capable of stopping an intrusion at a certain scale with a certain efficiency. Using different techniques, they would also collaborate internally to better fulfill the final objective. Detection and disinfection are based on the following rules.
Detection happens two ways:
- The software places canary files under certain folders and monitors them for changes. Canary files are like a canary in a coal mine: a sacrificial test to indicate a hazard. Canary files look desirable for ransomware to infect but are not actually valuable to the business.
- The software monitors systemwide file creation events and checks whether the new files being created (for a certain threshold value) are encrypted.
Based on the detection, if the encryption is an intentional act, the software throws a pop-up (with captcha) for the user to answer within a 10-second window. If the act is not intentional, the ransomware disinfection procedure kicks in and the Security Operations Center team is alerted to the attack.
Ransomware disinfection lines include:
- Querying handles quickly discover which process accessed the canary files. After checks based on the situation, the process is either quickly terminated or suspended. It’s fast but in situations where the ransomware uses multiprocessing techniques, it’s not able to detect all malicious instances initiated by the process.
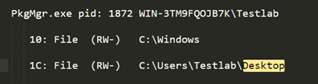
- Real-time monitoring of file system activity related to writing, deletion, and process creation of files provides more accurate information related to processes, along with details involved with encrypting the files. This covers situations where ransomware uses multiprocessing techniques.

- Parent-child relationship monitoring correlates with how different suspicious processes are connected. Parent-child relationships may be direct or indirect. A direct relationship exists when a file group has a direct line of descendants between parent and child file groups. All other file group relationships are indirect relationships. Parent-child relationship monitoring determines if there might be a situation in which the malicious parent process is not involved in encrypting the files directly, but rather its children are involved.
- Autoruns monitoring detects any malicious persistence mechanism used by the ransomware and removes posts from any persistence mechanism.
- Process-injection monitoring works when the driver, running in kernel mode, detects any malicious process injection used by the ransomware.
Once disinfection is complete, files that were encrypted during the detection and disinfection stage are restored. This is achieved when the driver, running in kernel mode, makes back-up files at a secure location before changes are made to them.
The final stage was testing if the software could protect a device from a ransomware attack. For this, the team accessed multiple private and publicly available ransomware samples. VMware IT performed the test on more than 500 different kinds of ransomware samples, such as testing the software against highly sophisticated ransomware (Petya) that was used to carry out a massive global ransomware attack. This malware targets Microsoft Windows-based systems, directing the main boot record to execute a payload that encrypts a hard drive’s file system table and prevents Windows from booting. It subsequently demands users to make a payment in Bitcoin to regain access to the system. As expected, our Roadblock software detected Petya and disinfected the system instantly, resulting in zero data loss, zero downtime, zero productivity loss, and no reputational harm.
Example of IT Stages of Software Development

Customizing Software Can Lead to New Marketable Products
Based on the process of developing customized software in successive phases, VMware IT Security has the potential to result in potentially marketable products, such as the RoadBlock ransomware protection software that will be released as a closed-source project, with the majority of the work already done.
For more information, watch the Roadblock Ransomware Protection demo.
VMware on VMware blogs are written by IT subject matter experts sharing stories about our digital transformation using VMware products and services in a global production environment. Contact your sales rep or vmwonvmw@vmware.com to schedule a briefing on this topic. Visit the VMware on VMware microsite and follow us on Twitter.



