By Vivek Achar, Senior Product Line Manager and Jay Thontakudi, Senior Product Marketing Manager
Many enterprises today operate in a distributed environment that spans different countries, regions, or continents. This includes applications that are either running on-premises in a data center or have migrated to the cloud. Today’s workforce is also widely distributed with a sizeable number of users working from home or a remote office. Productivity gets significantly impacted if users are unable to access these applications due to poor network conditions on local WAN links or when they are jostling for bandwidth with internet traffic. Security and compliance needs get compromised with the operational complexities of managing consistent policy implementation across distributed workloads.
VMware SD-WAN™, a network service of VMware SASE™, and Amazon Web Services (AWS) AWS Cloud WAN enable enterprises to overcome these challenges with a solution that is integrated to offer reliable, secure, scalable and efficient access to workloads on AWS, for users located anywhere. The solution ensures local presence with VMware SD-WAN services and offers global reach with the integration to AWS Cloud WAN riding over the AWS backbone. The solution gives enterprise IT operational simplicity to deploy large numbers of sites with easy on-ramp to the cloud and a rich user experience.
About AWS Cloud WAN
AWS Cloud WAN is a managed wide-area network (WAN) service that allows customers to easily connect and route their data centers, remote sites, and cloud applications over the AWS global network. The solution enables customers to build and operate their wide-area networks using simple network policies, removing the need to stitch together various networking, security, and third-party services. AWS Cloud WAN improves network security with built-in network segmentation capabilities that make it easier for customers to manage network isolation across their AWS or on-premises locations. It provides the control plane for how customer traffic flows through the AWS global network for their geographically dispersed use cases, making it possible to build high-performance, scalable, and secure wide-area networks in minutes.
AWS is a constant innovator of networking services that enable and simplify deployment and connectivity to cloud-based workloads. AWS Cloud WAN further pushes the envelope and helps customers to easily connect and route their data centers, remote sites, and cloud applications over the AWS global network.
About VMware SASE
VMware SASE is a cloud-delivered solution that ensures any user located anywhere and using any device can connect to AWS Cloud WAN in a secure, reliable, and efficient manner. The solution is delivered closer to the user by a global network of VMware SASE points of presence (PoPs). These PoPs offer an easy on-ramp to the AWS Cloud WAN. A major advantage with this approach is that the geographic diversity of the workforce does not impact the user’s experience while accessing applications.
VMware SD-WAN is the networking service of VMware SASE. It carries the user traffic on an overlay network built on top of existing WAN connections that include broadband, MPLS private lines, and 4G/LTE/5G. Conditions on WAN networks vary across different sites within an enterprise. The AWS and VMware solution automatically detects any deterioration in local WAN links related to loss, latency, and jitter, and dynamically remediates these conditions using Dynamic Multipath Optimization™ (DMPO) without any operator intervention. The solution helps enterprises limit investment in costly WAN links by augmenting bandwidth on their existing MPLS links with broadband connectivity, or by switching completely to broadband access.
VMware SASE delivers operational simplicity to help enterprises manage their distributed workforces using centralized orchestration. This approach eliminates the need for site-by-site configuration and management of remote user locations. The AWS and VMware solution uses AIOps to provide visibility into user experience when users access applications in the data center or on AWS. IT can ensure employee productivity without the need to be physically present at each location.
Network segmentation across VMware SD-WAN and AWS Cloud WAN
IT commonly uses network segmentation to reduce attack surfaces. This helps ensure users have access to only those services they are allowed to use and prevents a threat actor from moving laterally across the network if there is a breach. Network segmentation is also used to comply with industry regulations like PCI.
By using segmentation, customers can divide their network into logical sub-networks using the construct of a segment or Virtual Routing and Forwarding (VRF). Network segmentation allows traffic inside an enterprise to be segmented based on departments, lines of business or application types (example: IOT vs enterprise apps).
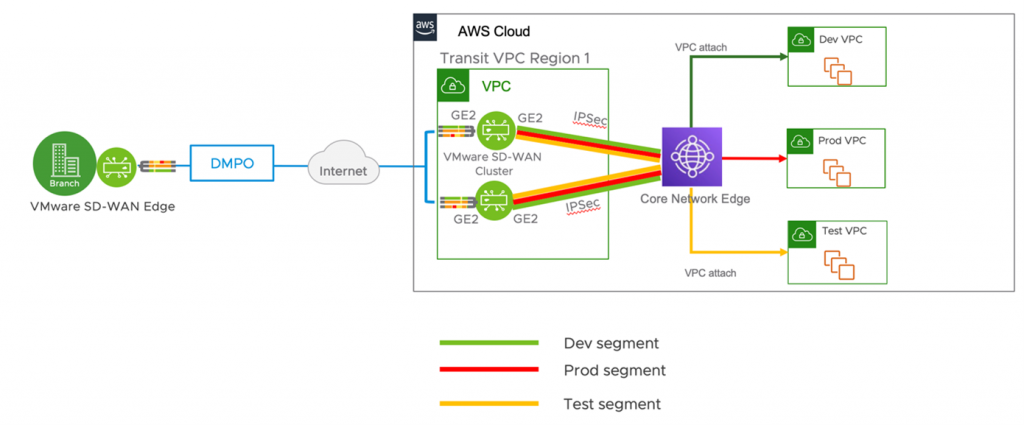
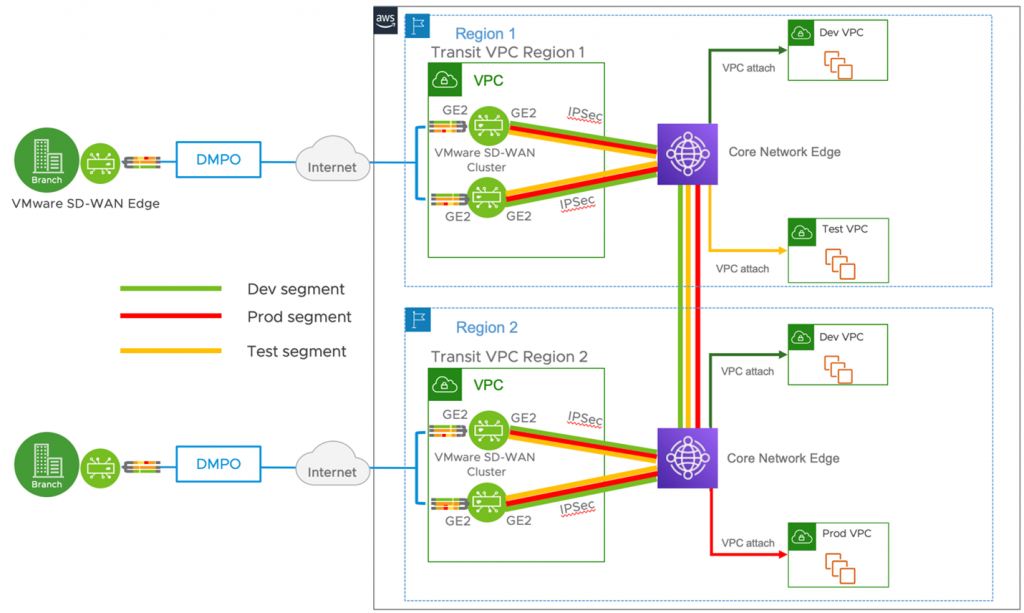
Managing network segmentation can become complex if there are inconsistencies or gaps in the solution. With VMware SD-WAN, enterprises can extend the segmentation they use in their data center to remote branch sites by using the segmentation capabilities built into VMware SD-WAN Edges. When enterprises transition to the cloud, they can extend that same network segmentation to their cloud workloads. With AWS Cloud WAN, customers can further extend the segmentation from their VMware SD-WAN fabric to their network on the AWS Cloud. This allows enterprises to ensure traffic isolation and data security end-to-end.
How to set up segmentation with AWS Cloud WAN
To use AWS Cloud WAN successfully, enterprises only need to take a few easy steps:
- Enterprise IT creates a ‘global-network’ segment which represents their overall private network (at a very high level).
- Under ‘global-network’, enterprise IT creates a ‘core-network’ segment, managed by AWS, as part of the global-network segment. Core-network includes regional connection points and attachments such as VPNs and VPCs, and it will operate in the regions defined by your core-network policy. Regional connection points (Core-Network-Edge) are created and managed by AWS as defined in the core network policy. The connection to the core-network is through the Core-Network-Edge.
- IT then attaches the VPC and subnet to a core-network and specifies the segment the VPC needs to be a part of
- Similarly, enterprises can connect the on-premises SD-WAN network where each VPN or AWS Connect attachment can be part of a segment
- Enterprise IT can replicate this in other regions to create a global network to extend segmentation across multiple regions
If enterprises have overlapping IPs across different segments, the same approach would work across AWS Cloud WAN.
AWS Cloud WAN also introduces the concept of route leaking across segments. For example: enterprise IT can assign a particular segment which can host shared resources, like a DHCP/DNS server, to be accessed by other parts of the organization residing in other segments. While the user defines the core-network policy, the AWS Cloud WAN allows you to specify if a segment can be a shared segment.
AWS Cloud WAN allows enterprises to define the core-network using a json file. Enterprise IT can define granular policies and customize behavior further according to network architecture demands.
Enterprises have regional or global presence across hundreds of branch locations and regional headquarters. As their cloud computing needs continue to grow, they can leverage the AWS ‘regions’ for regional sites to terminate. The example shown in the figure extends segmentation across AWS ‘regions’ leveraging the AWS backbone.
Steps to extend network segmentation from VMware SD-WAN to AWS Cloud WAN
The following steps can be configured on the centralized VMware SD-WAN Orchestrator to extend network segmentation across AWS Cloud WAN:
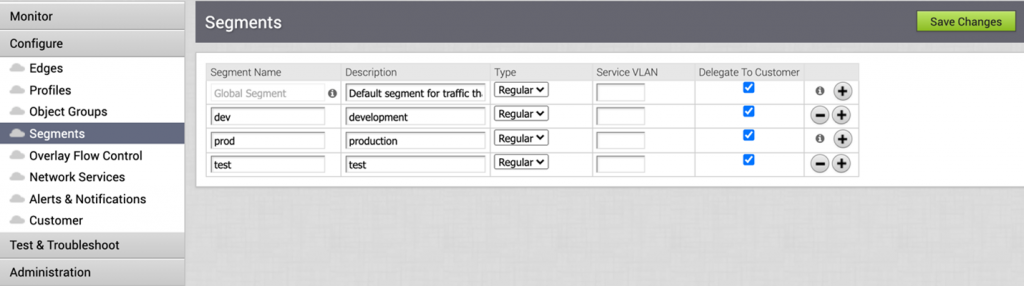
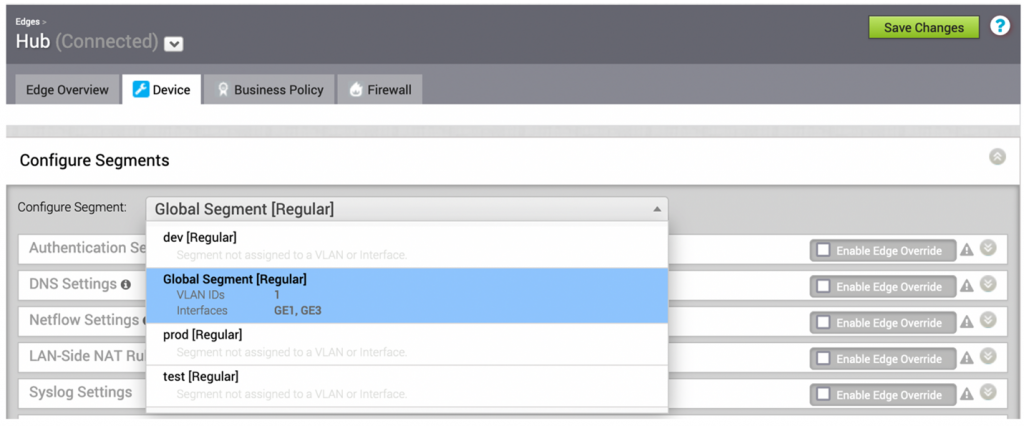
- For a greenfield deployment, enterprise IT can configure the segments that need to be extended into the AWS Cloud. For a brownfield deployment, the segments should have been created already.
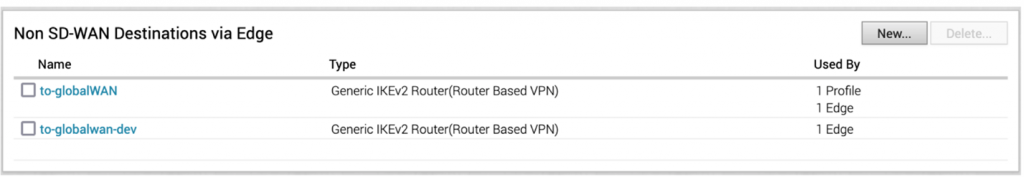
- Next, configure the Non SD-WAN Destinations tunnels needed for each segment
- Select the appropriate segments which need to be extended into the AWS Cloud
- Configure the Non SD-WAN Destinations tunnel for each specific segment
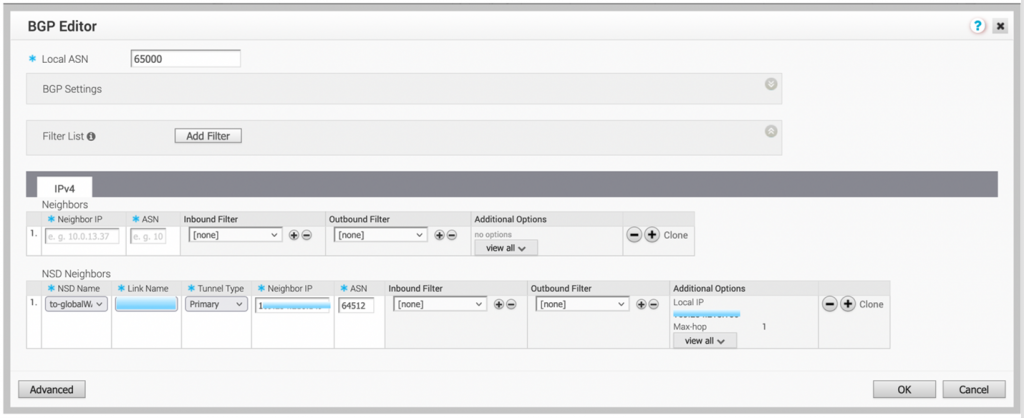
- Configure BGP. Once this is done, the local VMware SD-WAN Edge will advertise the routes it learned over the VMware SD-WAN fabric to AWS Cloud WAN and the Core-Network-Edge segment. The VMware SD-WAN Edge will learn the AWS Cloud subnets from Core-Network-Edge based on the AWS Cloud WAN policy configuration.
Simplified operations and a better experience for end users
To simplify operations, enterprise IT needs visibility into networks and insights into what users experience when they access applications. Enterprises can take advantage of the AWS Network Manager to gain visibility into the AWS Cloud WAN. Enterprises will also get insights into the state of the different attachments connected to their AWS Cloud WAN network. VMware SASE uses unified management capabilities to deliver visibility into the user experience of accessing applications, with fault isolation and proactive remediation capabilities that identify access problems and suggest how to fix them.
VMware’s collaboration with Amazon Web Services builds on our long-standing relationship. Together, the companies are providing a complete cloud services and cloud management portfolio that will give enterprise customers fast, flexible access to the cloud.
Learn more
- Learn more about our partnership on the VMware SASE and AWS web page
- Check out the AWS Cloud WAN web page
- Learn what’s new with AWS Cloud WAN
- Discover pricing
- Read the AWS blog, AWS FAQ, user guide, and API reference doc







